Please contact our sales department to receive individual terms for using the service
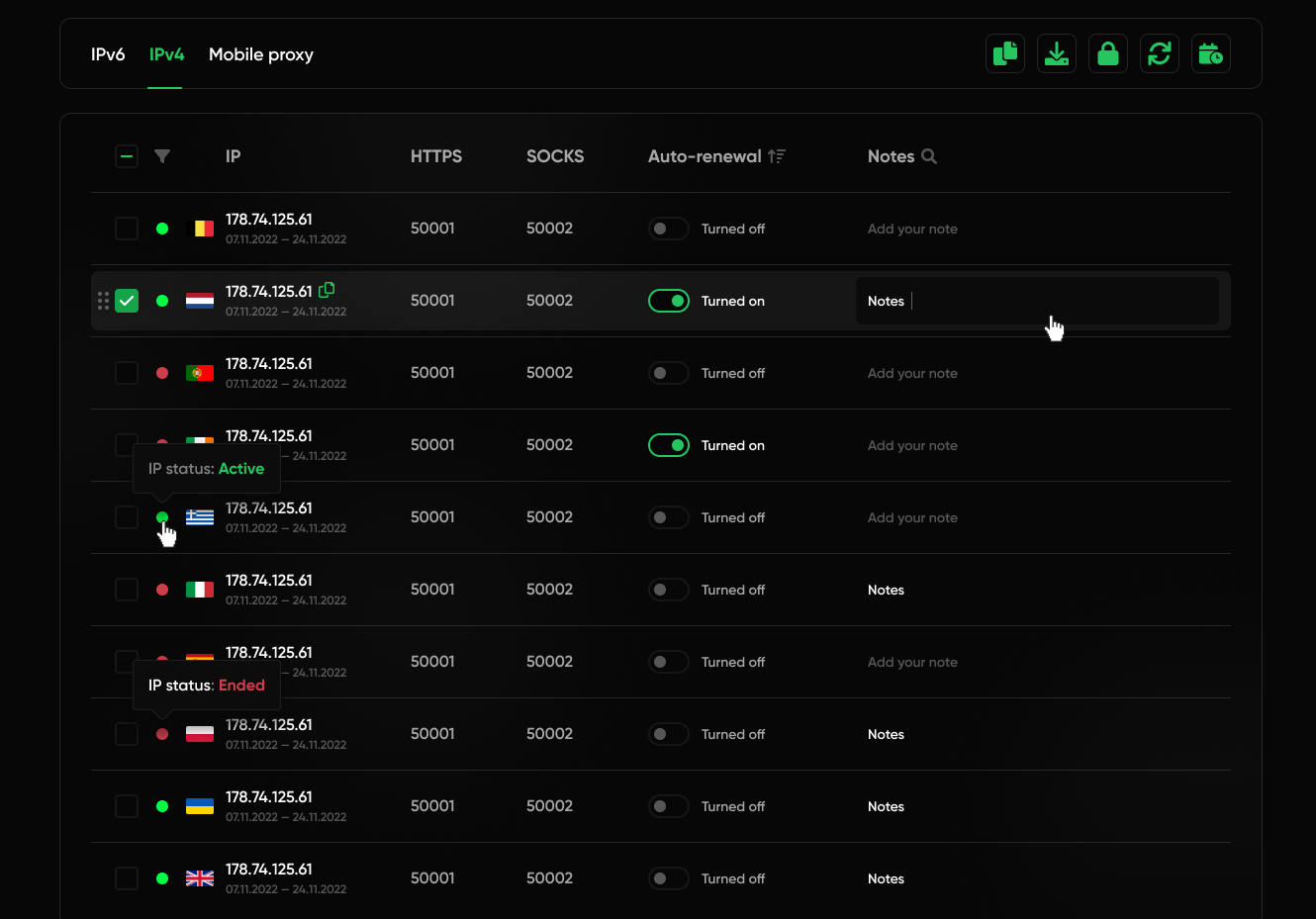
Simplified management of your proxies of Kazakhstan
- Automation via client API
- Balance and financial records
- Export in various convenient formats
- Commenting and categorizing proxies using folders
Check out the list of frequently asked questions, you may find yours.
Ask your question- How quickly is a proxy issued?A proxy can typically be selected and connected within a minute. However, if we need to verify that the use case doesn't violate our terms of service, the process may take longer.
- Do you offer proxies from a variety of cities in different countries?Yes, we provide proxies from a wide range of cities across various countries, including the USA, UK, India, Germany, France, Japan, and many others. Our extensive network allows you to select proxies from specific cities within these countries. For city-specific availability, please contact our support team, and we will ensure that your request is handled manually if the city is available.
- What advantages do premium and enterprise proxy solutions offer for businesses?Our premium and enterprise proxy solutions offer businesses the ability to handle large volumes of data with unlimited bandwidth. Custom proxy solutions are tailored to meet specific business requirements, providing a scalable and flexible approach to accomplishing required tasks.
- Do you provide elite proxies?We listen to user security requirements and provide the highest degree of encryption and anonymity. Our elite proxies meet criteria including a clean IP, not being listed on blacklists, and matching DNS records.
- What benefits do unlimited bandwidth proxies offer?Unlimited bandwidth proxies eliminate data transfer limits, allowing for continuous and high-speed execution of data-intensive operations and streaming services.
- How to access HTTP/s and SOCKS5 protocols proxy connections?Our proxies support both HTTP/s and SOCKS5. After purchasing a proxy, the provided IP address will feature two ports, each dedicated to connecting via the necessary protocol.
- Which Internet providers supply your ISP proxies?Our ISP proxies are sourced from leading ISPs such as Verizon, Windstream, Frontier, AT&T, and others.
- How do mobile proxies from providers like Verizon and Jio improve security?Our mobile proxies have real IP addresses from leading carriers such as AT&T, Verizon, Jio, T-Mobile, Vodafone, and others. These IPs are constantly rotating within real user networks, making them impossible to blacklist.
- What is the difference between static proxies and dynamic proxies?Static proxies keep one permanent IP address, which makes them suitable for long-term tasks that require a consistent identity. Rotating proxies, on the other hand, automatically change the IP at regular intervals, making them more effective for anonymity and bypassing restrictions. If you’re unsure which option suits your needs, our support team will be happy to assist you in choosing the best solution.
- Why did I purchase IPv6, but receive an IPv4 address?When you purchase, you get access to a pool of unique IPv6 addresses. All traffic is routed through our internal IPv4 server for stability and compatibility. Each connection is assigned its own port, which acts as an independent proxy, allowing you to run multiple sessions at once. Requests are transmitted over IPv6 and handled via IPv4 using tunneling, which ensures reliable performance and stable operation.
Cheap proxies of Kazakhstan for work
The proxies of Kazakhstan that we provide to our clients are free secure surfing on the network, which opens up huge opportunities for running business, personal interests and other types of public and private activities. Kazakhstan proxies allow you to bypass blocking on many resources and always remain anonymous. Our reliable equipment allows you to get the maximum level of freedom on the Internet and improve your online business for high stable profits in the future. The services provided by us are provided for individual use only.
One of the main factors of comfortable working with us is strict adherence to this rule: using a Kazakhstan proxy for brute forcing, spam and phishing is a very serious condtion violation that will have irreversible consequences, that leads with the urgent termination of our cooperation. Thus, we maintain the "purity" of the proxy of Kazakhstan for your effective work. If the listed conditions for using a personal IP are violated, you will be instantly blocked without the possibility of a refund.
Proxy of Kazakhstan: service features
The proxies of Kazakhstan offered by our service have a number of parameters that are of great importance for working on the network throughout the entire period of use:
- All proxies of Kazakhstan are sold individually.
We guarantee the absence of "neighbors" on the IP, during the entire lease term.
- HTTP/S and Socks5
Our IP supports both protocols and work in any browser, proxy, program or service.
- Speed channel - up to 1Gb/s
Dedicated speed for equipment in Kazakhstan
- UPTime 99%
Our equipment is under the round-the-clock supervision of specialists, which guarantees in case of a failure, the minimum amount of time for its elimination.
- Balancing
Equipment loads are balanced to ensure that failures are minimized.
- Minimum ping
Provides a proxy of Kazakhstan for individual use, which implies the absence of neighbors on the IP, makes it possible to get the minimum ping, where it is important, for example, in online games.
- Proxy of Kazakhstan scattered.
We understand how important it is to protect against the services' administration, for example, promoted accounts in social networks or betting on sport. According to this, when buying any number of IPs of a given geolocation, we will issue an IP address with a scatter across networks and subnets.
- No restrictions
We do not limit the speed and number of proxy threads and do not charge a fee for this.
- Convenient authorization
If possible, you can choose one of the two available authorization methods to the proxy: username + password, or by IP. Also, during the term, you can change the authorization method at any convenient time.
Advantages of buying a proxy of Kazakhstan from us
- Automation.
After choosing and paying for a proxy, connection and issuance takes place automatically, they are available in your personal account within a couple of minutes. - The minimum rental period.
We give the opportunity to test our services for a minimum period of 3 days. - The minimum purchase quantity.
We do not limit our clients to the minimum purchase quantity, you can purchase even 1 IP address from us. - Support 24/7/365.
Managers at any time of the day, without holidays and weekends, consulting services are ready, as well as a technical department will help by remote desktop access. - Сompensation.
Within 24 hours of a purchase, for any reason, you have the right to request a refund. - Savings.
On this basis, we have substantial permanent discounts with real savings of up to 40% on purchased addresses and extended lease periods. - Convenient payment methods.
Providing services all over the world, we offer online payment for the most popular payment methods: PayPal, Visa/MasterCard, WebMoney, AliPay, Qiwi Wallet. In the absence of the required payment system, you can ask for the possibility of accepting payment in a different way from our online consultants.






